Risk Assessment Methods – Training Course
What are Risk Assessment Methods?
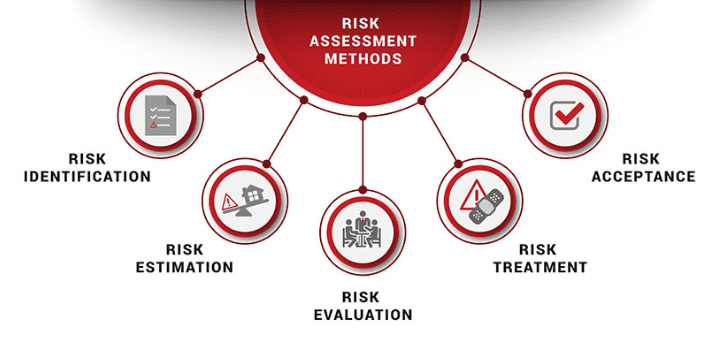
Understanding how to effectively assess risk may be a challenge for many industries. The risk assessment methods: OCTAVE, EBIOS, and MEHARI, will provide you with the sufficient knowledge on how to successfully identify and assess risk in your organization.
OCTAVE – Operationally Critical Threat, Asset, and Vulnerability Evaluation were developed by the Computer Emergency Response Team (CERT), and it was funded by the US Department of Defense. This risk assessment tool is used to help prepare organizations for security strategic assessments and planning for their information.
EBIOS – Expression des Besoins et Identification des Objectifs de Sécurité, was developed by the French Central Information Systems Security Division. The goal of this risk assessment tool is to assess and treat risks with an IS, which would result in assisting the management decision-making, and guide stakeholders to find a mutual set of discussions.
MEHARI – Methode Harmonisee d’Analyse de Risques, was developed by CLUSIF, a non-profit Information Security organization. The goal of this risk assessment tool is to mostly to provide guidelines for ISO/IEC 27005 Implementation and analyze scenario-based risks landscapes for short-long term security management.
Why are Risk Assessment Methods essential for you?
Our risk assessment methods training courses including the OCTAVE, EBIOS, and MEHARI methods, will provide you with the sufficient knowledge on how to successfully identify and assess risk in your organization. Risk Assessment Methods play a key role when it comes to protecting the business and its valuable assets. These methods will provide you with crucial guidelines on focusing on the risks that are more dangerous and that can have a huge financial and reputational damage for our business.
Benefits of Risk Assessment Methods
Being certified against Risk Assessment Methods helps you:
- To learn the concepts, methods, and practices allowing an effective risk management based on ISO 27005
- To put into practice the requirements of ISO 27001 on information security risk management
- To develop the skills needed to perform a risk assessment with the OCTAVE, EBIOS, and MEHARI techniques
- To obtain the ability to effectively guide organizations on the best practices in information security risk management
- To obtain the ability to effectively implement and manage an continuing information security risk management process
How do I begin with Risk Assessment Methods Training?
The objective and the outcome of the training will be to assist you in assessing risks using 3 methods, OCTAVE, EBIOS, and MEHARI. Through training, our tutors will guide you towards helping your business better the methods of risk assessments and protect the valuable assets.
PECB Certified Risk Assessment Methods training courses available now
Master the Risk Assessment Methods by attending the PECB Risk Assessment training course. By clicking in one of the options below, you can find the training that best suits to you and your career.
Why should you attend?
EBIOS Risk Manager training enables you to gain the necessary knowledge and develop the necessary competence to master risk management concepts and components related to all assets of relevance for Information Security based on the EBIOS method.
Based on practical exercises and case studies, you will have the opportunity to acquire the necessary skills to perform an optimal Information Security risk assessment and timely risk management by being familiar with its life cycle. This training fits perfectly in the framework of the ISO/IEC 27001 standard implementation process.
After mastering all the necessary concepts of risk assessment using the EBIOS method, you can sit for the exam and apply for a “PECB Certificate Holder in EBIOS Risk Manager” certificate. By holding a PECB Risk Manager Certificate, you will be able to demonstrate that you have the practical knowledge and professional capabilities to support an organization in performing risk assessment based on the EBIOS method.
Who should attend?
- Individuals seeking to learn and understand the basic concepts of Risk Management
- Individuals participating in risk assessment activities using the EBIOS method
- Managers seeking to understand the techniques for performing risk assessment based on the EBIOS method
- Managers seeking to master the techniques for analyzing and communicating the results of a risk assessment based on the EBIOS method
Learning objectives
- Understand the concepts and basic principles of risk management associated with the use of the EBIOS method
- Understand the activities of the EBIOS method in order to follow the completion of studies (pilot, control, reframe) as a work master
- Understand and explain the findings of an EBIOS study and its key deliverables
- Acquire the necessary skills to carry out an EBIOS study
- Acquire the necessary skills to manage security risks of an organization’s information systems
- Develop the necessary skills to analyze and communicate the results of an EBIOS study
Educational approach
- This training is based on both theory and best practices of risk assessment using the EBIOS method
- Lecture sessions are illustrated with examples based on case studies
- Practical exercises are based on case studies which include role playing and discussions
- Practical exercises and examples are similar to the Certificate Exam
Prerequisites
A fundamental knowledge of risk management.
Course Agenda
Day 1
- Training course objectives and structure
- Introduction to EBIOS RM method
- Workshop 1 Scope and security baseline
- Workshop 2 Risk origins
Day 2
- Workshop 3 Strategic scenarios
- Workshop 4 Operational scenarios
- Workshop 5 Risk treatment
- Closing of the training course
Day 3
- Certificate exam
Examination
The “PECB EBIOS Risk Manager” exam fully meets the requirements of the PECB Examination and Certification Programme (ECP). The exam covers the following competency domains:
Domain 1: Fundamental principles and concepts of Information Security risk management process based on the EBIOS method
Domain 2: Information Security risk management framework based on the EBIOS method
Domain 3: Information Security risk assessment using the EBIOS method
For specific information about exam type, languages available, and other details, please visit the List of PECB Exams and the Examination Rules and Policies.
Certification requirements
After successfully completing the exam, you can apply for the credential shown on the table below.
To be considered valid, these risk assessment activities should follow best implementation practices and include the following:
- Defining a risk management approach
- Designing and implementing an overall risk management process for an organization
- Defining risk evaluation criteria
- Performing risk assessment
- Identifying assets, threats, existing controls, vulnerabilities and consequences (impacts)
- Assessing consequences and incident likelihood
- Evaluating risk treatment options
- Performing a risk management review
General Information
- Certificate and examination fees are included in the price of the training course
- Training material containing over 200 pages of information and practical examples will be distributed
- An attestation of course completion worth 21 CPD (Continuing Professional Development) credits will be issued to the participants who have attended the training course.
- In case of exam failure, you can retake the exam within 12 months for free







